Think of your password as the key to your digital front door. Now, what if someone stole that key? That’s where two-factor authentication comes in. It's like having a second, constantly changing lock that only you can open. Even if a thief has your first key (your password), they're stopped cold at the second lock. This extra security layer isn't a luxury anymore; it's a fundamental part of keeping a modern business safe.
Your Digital Security's Second Lock

Two-factor authentication, or 2FA for short, is a security checkpoint that demands two separate forms of identification before granting access. Simply put, your password alone isn't enough anymore. You have to prove you are who you say you are with a second piece of evidence.
The whole point is to move beyond the old single-factor method (just a password) and build a much stronger defense against intruders. The magic of 2FA isn't just about adding a step; it’s about combining two different kinds of proof. This means that if a cybercriminal gets their hands on one—like your password—they still can’t get into your account without that crucial second factor.
The Problem With Passwords Alone
Let's be honest: relying only on passwords is a huge gamble. People often use weak, predictable, or recycled passwords across multiple accounts, leaving businesses wide open to attack. For a startling example, the password 'Eva' has shown up in over 7 million breaches, proving just how easy some passwords are to guess.
Two-factor authentication directly tackles this vulnerability. By creating a layered defense, it ensures that one stolen password doesn't spiral into a complete security disaster.
The numbers don't lie. Google has reported that adding SMS-based two-step verification can block 100% of automated bot attacks—the very tools behind most account takeovers. Requiring that second check-in dramatically shrinks the odds of a successful breach. You can find out more about these security statistics from recent studies.
Ultimately, the conversation around 2FA has shifted from if you need it to how you should implement it. It’s an effective and straightforward way to guard your most sensitive information, making it an absolute must-have for any business that takes its security seriously.
How Two-Factor Authentication Actually Works
Think of it like getting into a high-security bank vault. Your password is the key that gets you through the front door. But to open the actual vault, you need a second thing: a unique, one-time code the bank manager gives you right on the spot. That temporary code is your second factor.
Online, it’s much the same. When you type in your password, the service you’re logging into essentially says, “Okay, you have the key, but I need a bit more proof that it’s really you.” It then asks for that second piece of information—something only the real account owner should have. This creates a secure "digital handshake" to confirm your identity.
The Three Pillars of Authentication
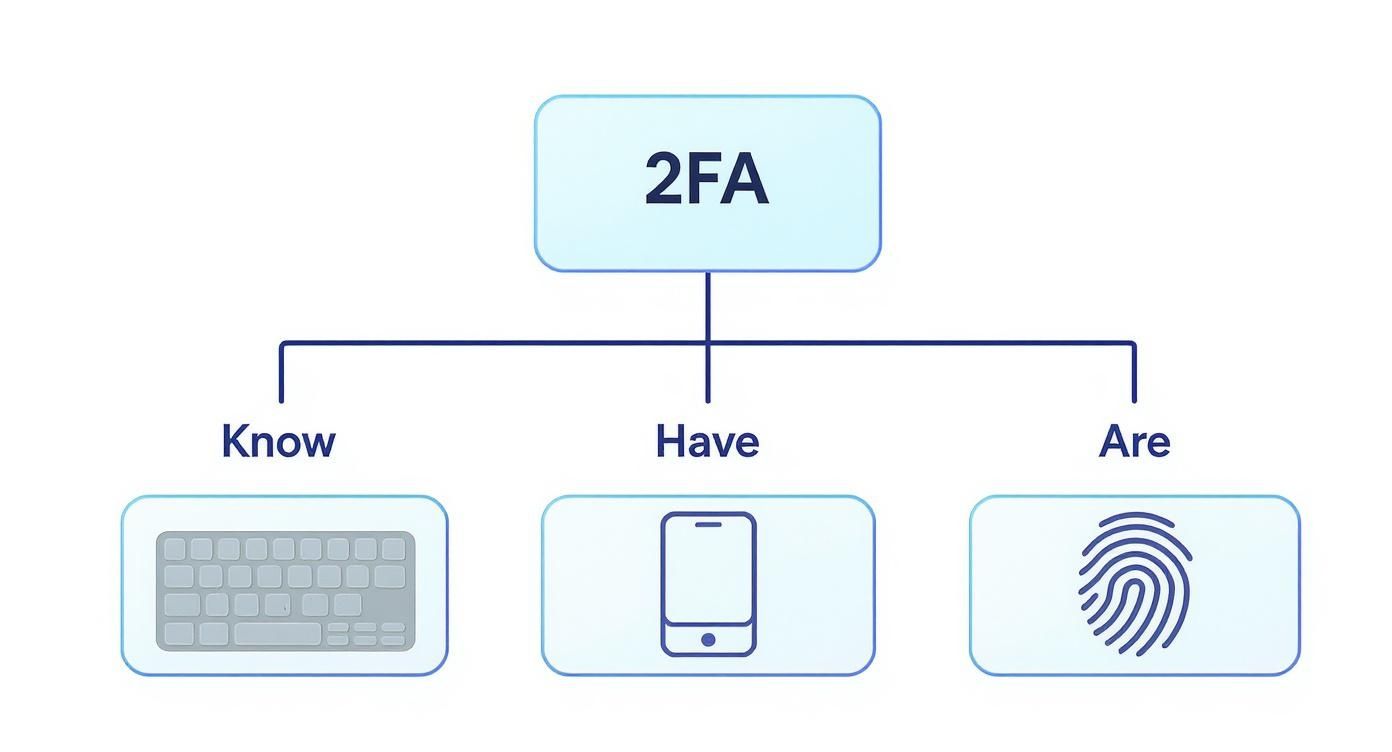
At its heart, 2FA works by mixing and matching two different types of credentials, known as authentication factors. The whole idea is to force you to prove your identity using two out of these three categories. This layered approach is what makes it so tough for an attacker to break in; they’d have to steal two completely different things instead of just one.
The three types of factors are:
- Something You Know: This is the classic. It’s any secret that’s supposed to be locked away in your brain, like a password or a PIN.
- Something You Have: This one is all about physical possession. It could be your smartphone (waiting for a code), a little hardware key like a YubiKey, or a company smartcard.
- Something You Are: This is the most personal category, relying on your unique biological traits. We’re talking about biometrics—your fingerprint, a facial scan, or even your voice.
By combining a password (something you know) with a code from your phone (something you have), 2FA builds a security wall that's far stronger than any password could ever be on its own.
What’s Happening Behind the Scenes?
When you first set up 2FA on an account, you’re registering your second factor—your phone number, an authenticator app, etc.—with that service. The service creates and stores a secret key that mathematically links your account to that specific second-factor device.
From then on, every time you log in, the process is simple and lightning-fast:
- First Factor: You enter your username and password as usual.
- Verification Challenge: The system checks your password. If it’s correct, it triggers the request for your second factor.
- Second Factor: You provide the one-time code from your app, tap "Approve" on a push notification, or scan your fingerprint.
- Final Verification: The system confirms this second piece of evidence. If everything matches up, you’re in.
The whole exchange takes just a few seconds, but it adds a massive layer of protection that pretty much neutralizes the risk of a stolen password.
Exploring The Different Types of 2FA
Not all two-factor authentication methods are created equal. Think of it like securing your home; a simple chain lock offers one level of protection, but a deadbolt and a security system offer something far more robust. When it comes to your business data, understanding the different types of 2FA is key to choosing the right balance of security and ease of use.
At its core, every 2FA method adds a second layer of verification on top of your password. This second layer is always based on one of two things: something you have (like your phone) or something you are (like your fingerprint).
This diagram breaks down the three core factors that can be combined for strong authentication.
The real strength of 2FA comes from mixing these categories. You combine something you know (your password) with either a physical item you possess or a unique part of you.
SMS and Email Codes
This is the one most people have encountered. You try to log in, and a one-time passcode (OTP) shows up in a text message or email. You type it in, and you're good to go.
It's simple and familiar, making it a popular choice for consumer-facing apps where convenience is a top priority. But there's a catch. SMS is widely considered the least secure form of 2FA. It's vulnerable to "SIM swapping," a nasty attack where a scammer convinces your cell provider to move your phone number to their device, letting them intercept your codes.
Authenticator Apps
Taking a big step up in security, we have authenticator apps. Think Google Authenticator, Microsoft Authenticator, or Authy. These apps generate a fresh six-digit code on your phone every 30 seconds or so.
To get started, you scan a QR code to link an account. From then on, the app generates a time-based one-time password (TOTP) entirely on your device. Because the code is never sent over a vulnerable network, it completely shuts down the risk of SIM swapping.
Authenticator apps hit the sweet spot for many businesses. They offer a huge security boost over SMS codes without forcing everyone to carry around a separate piece of hardware.
Hardware Tokens
When you absolutely need the highest level of security, you bring in the hardware. Hardware tokens are small physical devices, like a YubiKey, that plug into a USB port or tap on your phone using NFC.
There are no codes to retype. When prompted to authenticate, you just touch a button on the device. It handles the complex cryptographic handshake behind the scenes, making it incredibly fast and virtually phish-proof. These are perfect for protecting the "keys to the kingdom"—administrator accounts, financial systems, and access for key executives. The only real downside is the cost and making sure employees don't lose them.
Biometric Authentication
The final category is biometric authentication, which uses your unique physical traits. This is the Face ID on your iPhone or the fingerprint scanner on your laptop. It relies on who you are as the second factor.
Since this technology is built right into most modern devices, it's about as frictionless as it gets. It's also extremely difficult for a hacker to replicate your fingerprint or face, making it a powerful and convenient option.
Let’s quickly compare these methods side-by-side to see where each one shines.
Comparing Common 2FA Methods
| 2FA Method | Security Level | User Convenience | Best For |
|---|---|---|---|
| SMS/Email Codes | Low | High | Basic consumer accounts where ease of use is paramount. |
| Authenticator Apps | High | Medium | Securing most business accounts, cloud services, and internal tools. |
| Hardware Tokens | Very High | Medium | Protecting high-value targets like administrator access and financial systems. |
| Biometrics | High | Very High | Quick and secure logins on personal devices like laptops and smartphones. |
Choosing the right method often means mixing and matching. You might use a hardware token for your system administrators but find an authenticator app is the perfect fit for the rest of your team.
Understanding The Real Benefits and Risks
Rolling out two-factor authentication is one of the biggest security upgrades you can make, but it’s crucial to see it for what it is: a powerful layer in your security stack, not an impenetrable fortress. To build a defense that actually works, you need to understand what 2FA does brilliantly—and where its cracks can show.
The single greatest benefit is its ability to shut down credential-based attacks. Every day, massive password databases are leaked onto the dark web. Hackers scoop up these lists and use automated tools to try them against every login page they can find. With 2FA in place, a stolen password becomes almost worthless by itself. It protects your business from the ripple effects of data breaches that happen completely outside your control.
This is non-negotiable for any business with a remote or hybrid workforce. When your team is logging in from home networks, coffee shops, and airports, 2FA is the gatekeeper that confirms it's really them, dramatically cutting the risk of an outsider getting in.
The Clear Advantages of 2FA
The move toward 2FA isn't just a trend; it's a response to a clear and present danger. A huge number of companies have already deployed it, and more than half of all internet users have turned it on for at least one of their personal accounts. Why? Because it works. You can discover more insights about these global adoption rates on ElectroIQ.
Here’s what you gain:
- Blocks Unauthorized Access: This is its core job. An attacker can have the right password, but without that second piece of the puzzle, the door stays locked.
- Reinforces Password Hygiene: 2FA acts as a critical safety net for the inevitable weak password. For a complete strategy, see our guide on the best practices for password management.
- Protects Your Reputation: A data breach doesn't just cost money; it costs trust. Having 2FA shows you take security seriously, protecting both your data and your brand.
Being Honest About the Limitations
With that said, no security tool is a magic bullet. Motivated attackers are always looking for a way around defenses, and it's important to know what you're up against.
Two-factor authentication raises the bar for security immensely, but it doesn't eliminate the human element. Employee awareness and training remain critical pieces of the puzzle.
One of the most common vectors is phishing. A cybercriminal might build a pixel-perfect fake login page. If an employee is tricked into entering their username, password, and the six-digit 2FA code, the attacker grabs all three in real-time and uses them to log in to the real site.
Another major vulnerability, which mostly targets SMS codes, is SIM swapping. This is a social engineering attack where a scammer convinces your mobile provider to move your phone number to a SIM card they control. Once they hijack your number, they start receiving all your calls and texts, including any 2FA codes sent your way. This is a huge reason why authenticator apps and physical hardware keys are considered much more secure alternatives.
Putting 2FA to Work in Your Business

Knowing what two-factor authentication is and actually rolling it out across your business can feel worlds apart. But with a bit of planning, it’s a totally manageable—and crucial—security upgrade. The secret is to think of it less like a technical chore and more like a strategic business project.
It all starts with a clear policy. Before you flip a single switch, you need to be crystal clear on what you're protecting and why. A solid 2FA policy answers the tough questions upfront, ensuring everyone is on the same page from day one.
Building Your 2FA Deployment Roadmap
A successful rollout is a planned one. Just diving in can cause a lot of headaches, from frustrated employees to accidental security gaps. A much better approach is to phase it in, starting with your most critical assets.
Your roadmap should map out these key steps:
- Define Your Security Policy: Decide which systems and accounts absolutely need 2FA. Will you require it for everyone and everything? Or will you start with high-value targets like email, financial software, and key cloud accounts?
- Choose the Right 2FA Methods: Look back at the different types of 2FA. What makes sense for your team? You might find a mix-and-match approach is best—maybe hardware keys for your system admins and authenticator apps for the rest of the staff.
- Select a Vendor or Solution: Find a 2FA provider that plays nicely with the systems you already use, like your email service or Single Sign-On (SSO) platform. You'll want something that’s easy to manage and can grow with your company.
- Plan a Phased Rollout: Don’t try to do it all at once. Kick things off with a small pilot group, like your IT team, to smooth out any wrinkles. From there, you can expand to other departments, focusing first on those who handle the most sensitive information.
Ensuring a Smooth Employee Onboarding
Ultimately, your 2FA plan is only as good as your team's willingness to use it. If the process is confusing or clunky, people will see it as a burden, not the protective shield it's meant to be. That’s why clear communication and solid support are absolute must-haves.
A strong 2FA implementation is as much about people as it is about technology. Investing in employee training and support ensures that your security investment pays off by being used correctly and consistently.
To get your team on board, create simple, step-by-step setup guides. Run a few quick training sessions—even a 15-minute demo can work wonders—to show everyone how it works and, more importantly, why it matters. To build a stronger security culture overall, take a look at our cyber security tips for small business.
Finally, make sure everyone knows who to call when things go wrong. A lost phone or a login glitch shouldn't bring work to a halt. Having a clear support person or process in place keeps the frustration low and your business running smoothly.
For some businesses, two-factor authentication isn't just a good idea—it's the law. If you're in healthcare, finance, or a legal practice, you're not just handling data; you're the guardian of highly sensitive client and patient information. Regulations in these fields are strict, and implementing 2FA is one of the most direct ways to meet those non-negotiable standards.
Take a regulation like the Health Insurance Portability and Accountability Act (HIPAA), for instance. HIPAA demands that healthcare providers put strong technical safeguards in place to control who can access electronic protected health information (ePHI). A simple password just doesn't cut it anymore and is no longer seen as doing your due diligence.
Proving Your Commitment to Security
Adopting two-factor authentication gives you a clear, documented record showing you're taking real steps to lock down your data. It’s tangible proof for auditors that you have strong access controls, which is a fundamental piece of almost every data privacy law out there.
The stakes are incredibly high, and they go way beyond just stopping a data breach. If you fail to meet compliance standards, you could be looking at crippling fines, legal battles, and a loss of client trust that you might never get back. 2FA is a foundational control that shows everyone you’re serious about security.
This is the point where 2FA stops being just a tech tool and becomes an essential business strategy. It helps your organization:
- Satisfy Regulatory Requirements: It directly answers the call for strong authentication in frameworks like HIPAA and the Payment Card Industry Data Security Standard (PCI-DSS).
- Avoid Costly Penalties: You significantly lower the risk of non-compliance fines, which can easily climb into the thousands or even millions of dollars.
- Build Client Trust: It’s a powerful signal to your clients and partners that you put the security of their confidential information first.
Getting a handle on your current security posture is the right place to start. A great way to do that is by using this comprehensive IT security audit checklist to find any weak spots in your defenses. By making 2FA mandatory, you’re not just adding another security layer—you're satisfying auditors and protecting the future of your business.
Putting It All Together With Expert Help
We’ve covered a lot of ground, and it’s clear that two-factor authentication is one of the most effective ways to slam the door on unauthorized access. But knowing what 2FA is and actually getting it rolled out across your business are two very different things. It’s easy to feel stuck, and that’s where getting some expert help can make all the difference.
Think of it this way: you wouldn't rewire your office without an electrician. Implementing security is no different. A seasoned IT partner takes the guesswork out of the equation, helping you sidestep common pitfalls and costly mistakes. They can help you figure out the best approach for your team, whether that’s an authenticator app for daily use or more robust hardware tokens for those with the keys to the kingdom.
Taking the step from knowing about 2FA to actively using it is where true security begins. A guided implementation ensures your investment in this technology is effective from day one, protecting your most critical assets without disrupting your workflow.
Let an Expert Handle the Heavy Lifting
When you partner with an IT provider like GT Computing, you don't have to become a cybersecurity guru overnight. We dive into the technical details so you can stay focused on running your business, all with the confidence that your digital front door is locked down tight.
Here’s a look at how we approach it:
- Security Assessment: First things first, we pinpoint your most sensitive systems and data to figure out what needs protecting the most.
- Solution Deployment: We'll help you choose and set up a 2FA solution that plays nicely with the software you already use every day.
- Ongoing Management: Security isn't a "set it and forget it" task. We stick around to provide support and make sure your defenses stay strong as new threats emerge.
Let us help you build a stronger, more secure foundation for your business.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com



