Think of your company's network as a single, large, open-plan office. While it might seem efficient, it means a minor issue—like someone spilling coffee on a power strip—could potentially knock out the electricity for the entire floor. The same is true for your digital workspace. A "flat" network, where every device can talk to every other device, is a huge, unnecessary risk.
Network segmentation is the digital equivalent of putting up walls to create separate, secure rooms within that office. It’s a foundational security strategy that involves dividing your computer network into smaller, isolated sections. This simple act of creating digital boundaries contains threats, boosts performance, and is one of the most effective ways to protect your business's sensitive data.
What Is Network Segmentation Really
Let's use a more vivid analogy. Imagine your business is a large bulk carrier ship. A flat network is like a ship with one giant, open cargo hold. If a small leak springs anywhere in the hull, the entire vessel can flood in a hurry, taking all its valuable cargo down with it.

Network segmentation is the process of installing watertight bulkheads in that ship, creating multiple, sealed compartments. Now, if one compartment takes on water—let's say a ransomware attack hits one part of your network—the damage is completely contained. The rest of the ship stays afloat, and your operations can continue.
From Fragile to Resilient
This simple shift in thinking moves your network from a fragile, all-or-nothing system to a resilient and secure one. In a flat network, one employee clicking a phishing link could infect their laptop, which then spreads malware to your accounting servers, customer databases, and point-of-sale systems within minutes.
With proper segmentation, that infected laptop is confined to a general-use segment, completely walled off from the critical server segment where your financial data is stored. The attack is stopped dead in its tracks.
This entire strategy hinges on a core security concept: the principle of least privilege.
The principle of least privilege dictates that a user or device should only have the absolute minimum levels of access—or permissions—needed to perform its specific function. Nothing more.
Segmentation is how you actually enforce this principle across your network. You're no longer simply trusting users and devices to do the right thing; you're building a system where trust isn't a prerequisite for security. To get a better handle on the hardware and software that form these digital walls, it helps to understand what network infrastructure is and how all the pieces fit together.
The Core Benefits for Your Business
Moving away from a flat network brings immediate, tangible benefits that extend well beyond just security. In fact, think of segmentation as a key part of your business continuity plan.
Here’s a quick overview of what you stand to gain by implementing network segmentation.
| Benefit | Impact on Your Business |
|---|---|
| Improved Security | Contains breaches to a small area, dramatically reducing the "blast radius" of a cyberattack. A hacker in one segment can't easily move laterally to compromise your whole operation. |
| Better Performance | Isolates high-bandwidth traffic (like video calls or data backups) from apps that need stable performance (like VoIP phones), reducing network congestion for everyone. |
| Simplified Compliance | For businesses governed by regulations like HIPAA or PCI DSS, segmentation offers a clear, auditable method to prove you are isolating and protecting sensitive information. |
This table shows that segmentation isn't just a technical task—it's a strategic move to build a stronger, more dependable business.
Ultimately, understanding what network segmentation is means seeing it not as an IT chore, but as a proactive decision to make your business ready to weather any digital storm.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com
Why a Flat Network Is a Business Risk
Alright, enough with the technical theory. Let's get down to what really matters: what happens if you don't segment your network? The answer is unfortunately simple. A flat network—where every single device can freely talk to every other device—is a ticking time bomb for any business.
Think of it as an open-plan office with no walls or locked doors. If one person gets sick, everyone gets sick. In the digital world, this design means one small security mistake can set off a catastrophic chain reaction. It’s not a question of if a threat gets in, but when—and on a flat network, there’s nothing to stop it from spreading everywhere.
The Wildfire Effect of a Single Breach
Let’s put this in the context of a law firm or a dental practice. You handle incredibly sensitive data every day, from client case files to patient health records. Now, picture a common, innocent-looking event: an employee brings their personal laptop to work and connects to the office Wi-Fi.
What no one knows is that the laptop is carrying a ransomware infection. On your flat network, that malware instantly starts looking around for new targets. It doesn't take long to find the main server—a goldmine of valuable files—and it begins encrypting everything it can reach.
Before you’ve even had your lunch break, your entire operation could grind to a halt.
- Client files are held hostage. Suddenly, you're at risk of missing legal deadlines and compromising confidential case data.
- Patient records become inaccessible. You can’t schedule appointments, look up medical histories, or provide critical care.
- Billing and accounting systems are frozen. Invoices stop going out, payments can’t be processed, and your revenue stream dries up.
This isn't some made-up horror story; it's a grim reality for businesses that overlook this fundamental risk. A flat network is what turns one small infection into a complete business shutdown.
Segmentation as Your Digital Circuit Breaker
This is precisely where network segmentation proves its worth as a core business continuity strategy. Let’s replay that same scenario, but this time on a segmented network. The system is designed like an electrical panel with multiple circuit breakers.
When the infected laptop connects to the “Guest” network segment, the ransomware’s attack is dead on arrival.
The malware is trapped inside its designated segment, completely blocked from even seeing the firewalled-off "Servers" segment or the "Employee Workstations" segment. The blast radius is contained. Your critical business operations are untouched and continue running securely.
This containment is the single most powerful reason to move away from a flat network. It turns a potential catastrophe into a minor, easily managed incident.
A Lesson from a National Crisis
The push for segmentation isn't just an IT best practice; it became a national priority after major cyberattacks revealed just how vulnerable flat networks are. The 2021 Colonial Pipeline ransomware attack is a perfect, chilling example. Hackers found a way into the business network and, due to poor internal segmentation, moved sideways into the operational network. The result? They shut down fuel supplies for the entire U.S. East Coast.
The attack caused widespread panic and resulted in economic losses estimated at a staggering $4.4 billion. The fallout was so severe that it triggered a federal mandate for stronger cybersecurity, drastically changing how industries like healthcare and legal must approach data protection. You can find more about the growing demand for these solutions in market analysis from sources like Wise Guy Reports.
This event was a wake-up call for everyone, proving that a weak internal structure is just as dangerous as a weak perimeter. Segmentation is no longer a simple IT upgrade; it’s fundamental to protecting your revenue, your reputation, and your very ability to operate. Without it, you’re not just leaving the front door unlocked—you’re leaving all the internal doors wide open, too.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com
How Network Segmentation Works: The Tools of the Trade
Alright, we've established the serious risks that come with a flat network. So, what's the solution? Let's get into the "how" of building a smarter, more secure network. Implementing network segmentation isn't about flipping a single switch; it's a strategy that uses a few core tools to build those digital walls we talked about.
Think of these techniques as the essential tools in an IT expert's toolkit. While the backend can get technical, the concepts themselves are pretty straightforward. Getting a handle on them will help you have much more meaningful conversations about your company’s security and the protections being put in place.
The image below shows exactly why a flat network is so dangerous. A single point of failure can give an attacker a direct line to your most critical assets.
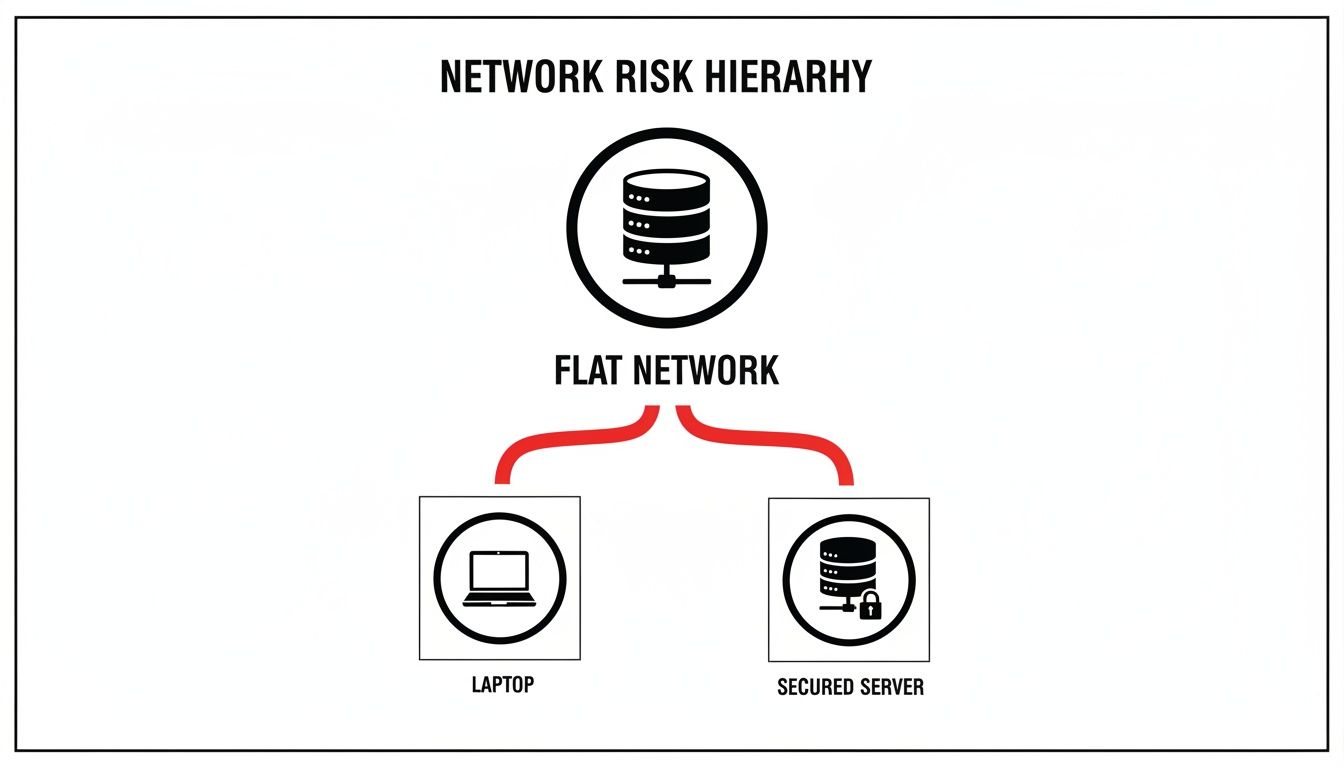
You can see how malware on one laptop has an open highway to attack a sensitive server. It’s the perfect recipe for a digital wildfire. In a properly segmented network, firewalls would block that path, containing the threat immediately.
H3: VLANs: Creating Virtual Departments
One of the most common and effective tools in the box is the Virtual LAN (VLAN). Your physical office network is a Local Area Network (LAN). VLANs allow a tech provider to take that one physical network and digitally slice it into multiple, isolated virtual ones.
It’s like having your entire company on one open-plan office floor. Using VLANs is like putting up walls to create separate departments—Sales, Accounting, HR, and a lobby for Guest Access. To get into Accounting, you need an "Accounting" keycard. A guest's keycard won't work.
That’s precisely how VLANs operate. Devices on the guest WiFi VLAN are completely separated from the server VLAN. They can't see or talk to those critical devices, even though they might be plugged into the same physical network switch.
H3: Subnetting: Assigning Unique Digital Addresses
Another core technique is subnetting. If VLANs are the separate departments, subnetting is like giving each of those departments its own unique block of mailing addresses. This process involves breaking up your large network into smaller, more organized sub-networks, or subnets.
Every piece of data zipping across your network is a "packet," kind of like a letter in the mail. Subnetting ensures that packets addressed to the "VoIP Phones" subnet only go there, keeping them from clogging up the network for the "Employee Workstations" subnet.
This logical separation helps manage traffic flow, boost performance, and adds another security layer by controlling communication between these address groups. The rules for what can pass between subnets are enforced by your firewall. To get a better sense of how these devices act as traffic cops, check out our guide on finding the best firewall for your small business.
H3: Comparing Segmentation Methods: VLANs vs. Subnets vs. Microsegmentation
To help you visualize how these common techniques fit together, here's a quick comparison. Each method serves a different purpose, ranging from broad-level organization to highly granular, per-device security.
| Technique | How It Works | Best For |
|---|---|---|
| VLANs | Creates isolated virtual networks on a single physical network. Like creating separate, locked departments in an office building. | Grouping devices by function or trust level (e.g., Guests, Employees, Servers). |
| Subnets | Divides a network into distinct address ranges. Like assigning unique postal codes to different departments. | Improving network performance, organizing traffic flow, and creating basic access control between large groups of devices. |
| Microsegmentation | Applies security policies to individual workloads or devices. Like assigning a personal security guard to every single person and computer. | High-security environments, protecting critical applications, and preventing lateral movement by attackers (Zero Trust). |
While VLANs and subnets are the foundational building blocks for most small business networks, microsegmentation represents the next step up in security, offering a far more robust defense.
H3: Microsegmentation: The Ultimate Security Detail
Where VLANs and subnets group devices into broad categories, microsegmentation zooms in to a much, much finer level. This is a more modern approach that aligns perfectly with a Zero Trust security mindset.
Think of microsegmentation as assigning a dedicated, personal security guard to every single device on your network—not just every department. Every server, every workstation, even every printer gets its own guard with a very strict list of who it's allowed to talk to. Everything else is blocked by default.
The power here is immense. Even if a hacker breaches a trusted segment—say, they get onto the "Servers" VLAN—microsegmentation stops them cold. They can't jump from that first compromised server to another one because each server's personal "guard" blocks the unauthorized connection. It isolates workloads from each other, crushing an attacker's ability to move laterally.
For any business handling sensitive data, microsegmentation provides the strongest internal security you can get. To put these powerful tools to work correctly, it’s vital to follow established network segmentation best practices.
By layering these methods, an IT partner like GT Computing can construct a defense-in-depth strategy that truly protects your business from the inside out.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com
Building Your Network Segmentation Plan
It’s one thing to understand the dangers of a flat network and the tools used to fix it. It's another thing entirely to put a solid plan into action. Rolling out network segmentation isn't a quick, one-off task; it's a careful, structured process. You need a clear roadmap to make sure every digital wall goes up in exactly the right place.

Think about it like designing a high-security building. You wouldn't just start throwing up walls at random. First, you'd figure out what you need to protect, classify its value, define who gets access, and then you'd build the barriers. The process for network segmentation follows the same common-sense logic.
Step 1: Discovery and Mapping Your Assets
Everything starts with Discovery. You simply can't protect what you don't know you have. This first phase is all about creating a complete inventory of every single device connected to your network.
And I mean everything. This isn't just about computers and servers. We're talking VoIP phones, printers, security cameras, and even those smart thermostats in the breakroom. The goal is to get a complete, bird's-eye view of your entire network.
This is a non-negotiable first step. So many security breaches happen because of some forgotten, unmanaged device tucked away in a corner. Without a full map, you’re trying to build a fortress with gaping, invisible holes.
Step 2: Classification by Risk and Function
Once you have that complete inventory, you move on to Classification. This is where you start grouping your assets based on their role, the sensitivity of the data they handle, and their overall trust level. In essence, you’re deciding which devices belong in which "secure room."
Common groupings often include:
- Critical Infrastructure: Think servers holding financial data, client records, or patient files. These are the crown jewels and need the tightest security.
- Employee Workstations: The desktops and laptops your team uses for daily work.
- Guest Access: A totally separate, walled-off segment for visitors, personal phones, and any other untrusted connections.
- IoT Devices: Internet of Things gadgets like cameras, smart locks, or HVAC systems that are notoriously insecure.
This classification work becomes the blueprint for your network's new architecture. It tells you exactly where the digital walls need to go as you design a network that delivers business value.
Step 3: Policy Creation and Defining the Rules
With your assets neatly grouped, it's time for Policy Creation. This is where you write the specific rules that control how—or if—these new segments can communicate with each other. This step answers the crucial question: "Who is allowed to talk to whom?"
The core principle here is zero trust. By default, no segment is allowed to communicate with any other segment. From there, you explicitly create "allow" rules only for traffic that is absolutely essential for business.
For example, your employee workstations probably need to access the file server, so you’d create a rule permitting that specific traffic. The Guest WiFi, on the other hand, should have a rule that strictly blocks it from accessing anything on your internal network, giving it a direct line only to the internet. If you have a remote team, you'll also need a clear policy to secure remote access to the right resources.
Step 4: Implementation and Continuous Monitoring
Finally, we get to Implementation and Monitoring. This is the hands-on part where an IT partner like GT Computing actually deploys the VLANs, sets up the subnets, and configures the firewall rules according to the plan. But the job isn't done when you flip the switch.
Network segmentation is never a "set it and forget it" project. It’s a living system. New devices get added, business needs evolve, and new threats appear daily. Constant monitoring is the only way to ensure the rules are working as intended and to spot any strange activity that could be the start of an attack.
Sadly, this is where many organizations drop the ball. While one survey found that 96% of organizations said they used segmentation, a staggering 75% of them only segmented two or fewer critical areas. This created a huge problem during the pandemic, as 43% of firms hadn't updated their segmentation in two years, a failure that directly correlated with a spike in ransomware spreading laterally across their networks. This data is a stark reminder of why a dedicated, managed approach is so critical for real security.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com
Meeting Compliance Demands with Segmentation
For businesses in regulated industries like healthcare, finance, or law, compliance isn't just a good idea—it's the law. You're handling incredibly sensitive information every single day, and the consequences of a slip-up are severe. This makes sticking to regulations a non-negotiable part of doing business.
In these environments, network segmentation shifts from a "nice-to-have" security feature to a "must-have" compliance tool. It becomes a critical way to meet strict standards like HIPAA for healthcare providers or PCI DSS for anyone who processes credit card payments.
Providing a Clear Audit Trail
When an auditor shows up, they aren't there to hear about your good intentions. They need to see hard, physical proof that you're actively protecting sensitive data. A properly segmented network gives them exactly that.
By carving out dedicated, locked-down zones for different types of information, you build a network architecture that’s easy to explain and defend.
- Protected Health Information (PHI): Any device that touches patient data—from a front-desk PC to a server storing medical records—gets placed in its own highly restricted HIPAA segment, firewalled off from everything else.
- Cardholder Data Environment (CDE): In the same way, any system involved in payment processing is isolated into a PCI-compliant segment. This drastically shrinks the area an auditor needs to scrutinize.
- Guest and Public Access: Your public WiFi is kept in its own sandbox, with absolutely no path for a visitor's smartphone to even see your internal systems.
This kind of setup immediately shows you’re taking your responsibilities seriously. It creates a clear, visible audit trail that demonstrates precisely how and where regulated data is secured, which is a huge step toward satisfying any compliance framework.
An auditor can instantly see that you have created specific, contained "safe zones" for regulated data. This verifiable separation is often one of the first things they look for to confirm due diligence.
Reducing the Scope and Cost of Compliance
One of the biggest wins from a compliance perspective is scope reduction. Take a PCI DSS audit, for example. Without segmentation, you’d have to prove that every single device on your network meets its tough security standards. That’s a massive, expensive headache.
With segmentation, those strict controls only have to be applied to the small segment containing cardholder data—the CDE. This makes achieving and maintaining compliance simpler, faster, and much easier on your budget. You can focus your strongest (and most expensive) security efforts where they're actually needed.
For GT Computing's clients, implementing segmentation with Cisco or Meraki gear means isolating patient data from guest WiFi, ensuring HIPAA compliance and slashing breach costs by up to 60% in penalties. It's a strategy driven by real-world needs, and you can see its impact across the industry in current network security spending trends. It's not just a technical fix—it’s peace of mind for your practice.
Think of network segmentation as a critical investment in risk management. It dramatically lowers your exposure to crippling fines, legal battles, and the reputational damage that a data breach always leaves behind. When protecting client and patient data is everything, segmentation is how you prove you're up to the task.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com
Let's Build Your Secure Network Together
You now have a solid grasp of what network segmentation is and why it's so critical for protecting your business. But knowing what to do and knowing how to do it are two very different things. Designing and implementing a segmented network properly takes a specific skill set, specialized tools, and a lot of experience.
That’s where we come in.
At GT Computing, we live and breathe this stuff so you don't have to. We handle the technical heavy lifting, taking the entire burden of network security off your shoulders. This frees you up to do what you do best: run your business.
Our Hands-On Managed Security Approach
We don't sell cookie-cutter solutions. Our process starts with a simple conversation to understand your business, your team's workflow, and your unique security concerns.
- Custom Blueprint: First, we map out your entire digital operation. We identify who needs access to what and design a custom segmentation plan that fits your business like a glove, ensuring you meet any compliance rules along the way.
- Professional Build-Out: We use top-tier, professional-grade equipment from trusted industry names like Ubiquiti, Cisco, and Meraki to build your network. This isn't just about security; it's about creating a fast, stable, and reliable foundation for your daily work.
- Ongoing Partnership: Our job isn't done once the system is live. We're your long-term IT partner, providing managed services to monitor your network, perform maintenance, and adapt your defenses as new threats pop up and your business grows.
Think of us as your in-house IT department. We build and maintain the digital walls that protect your company, so you can stop worrying about security and focus on growth.
Partnering with an expert for network segmentation isn't an expense—it's a strategic investment in your company's stability and security. It protects your data, keeps you compliant, and gives you invaluable peace of mind.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com
Answering Your Questions About Network Segmentation
Even after seeing the benefits, it's natural for business owners to have questions about how network segmentation will work in the real world. Let's tackle some of the most common ones head-on.
Is Network Segmentation Too Expensive for My Small Business?
This is a fair question. While there's an initial cost, it's almost always a fraction of what a serious data breach would cost you in lost revenue, fines, and reputation. The good news is that modern, professional gear from companies like Ubiquiti puts powerful segmentation tools well within reach for small and mid-sized businesses.
Think of it less as an expense and more as an investment that pays you back. Beyond security, you'll often see a tangible return in better network performance and far less time spent troubleshooting mysterious slowdowns.
Will Segmenting My Network Slow It Down?
It’s a common myth, but the reality is usually the exact opposite. A well-designed segmented network almost always improves network performance, sometimes significantly.
By creating separate "lanes" for your network traffic, you stop different systems from fighting over bandwidth. This means your VoIP phone system won't get choppy just because someone is uploading a huge file, and your point-of-sale system stays responsive during peak hours. The result is a faster, more reliable network for everyone.
How Do I Know What to Segment?
The best way to start is by thinking about your business logically. Group your devices and users based on what they do and how much you trust them. This simple approach creates the foundation for a much stronger network.
The most effective segmentation plans often begin with creating a few key groups. An experienced IT partner like GT Computing can conduct a full discovery process to map out all your assets and create a logical and secure plan tailored for you.
Here are a few common segments we create for businesses:
- Critical Servers: This is where you lock down your most sensitive data, like financial records or client information.
- Employee Workstations: The day-to-day computers your team relies on.
- Guest Wi-Fi: A completely walled-off zone for visitors, personal phones, and other non-company devices.
- IoT Devices: A separate area for things like security cameras, smart thermostats, or printers that don't need access to sensitive company data.
Is a Firewall Enough Without Segmentation?
A firewall is absolutely critical—it's the guard at the main gate, protecting you from the open internet. But what happens if a threat gets past the gate? Maybe it came in on an employee's infected laptop or a malicious USB drive.
That's where segmentation shines. It provides security inside the walls, creating internal barriers that stop an intruder from moving freely across your network. A single compromised device becomes a contained incident, not a company-wide disaster. For a truly layered security posture, you absolutely need both: a strong firewall at the edge and smart segmentation on the inside.
Keep your business running without IT headaches.
GT Computing provides fast, reliable support for both residential and business clients. Whether you need network setup, data recovery, or managed IT services, we help you stay secure and productive.
Contact us today for a free consultation.
Call 203-804-3053 or email Dave@gtcomputing.com



